DELAWARE – The internet security firm Wordfence has sent out alerts warning Gmail users of what they call a “highly effective phishing attack.”
The entry on their site was originally posted on January 12, but has been updated with new details from Google. The site reports that experienced tech people have been hit by the attack and have fallen for it.
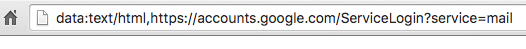
The site says that the attacker sends you an email to your Gmail account, from someone you know who has already been hacked. It includes an image that looks like an attachment from the sender, but when you click on the image, a new tab opens, prompting you to sign in again to Gmail. In the location bar you see “accounts.google.com”.
After you sign in, you are compromised. According to a commenter on Hacker News, the attackers then log in to your account and use your attachments and one of your subject lines and start sending out more phishing requests to your contact list. And, of course, once they are in your account, they could reset your password and do other things online in your behalf.
Experts say that enabling two-step verification on your account is helpful.
For more details, visit the Wordfence web site here.

